The Cybersecurity Assurance and Digital Trust team is responsible for enabling innovative and resilient solutions to meet the evolving cybersecurity and privacy needs of the UMBC community.
Quick Links
Staying current with IT Security Notices
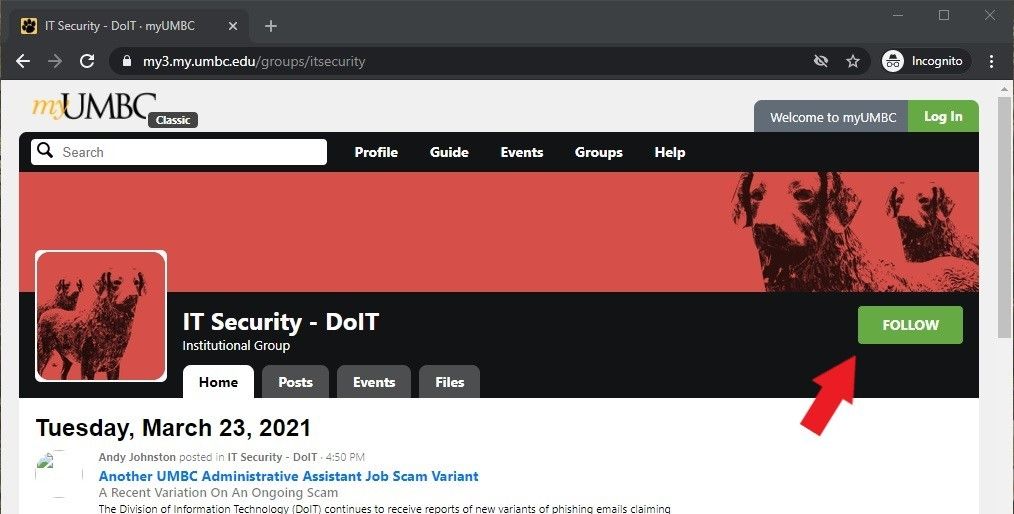
The DoIT Security Group posts notices and articles about threats, scams, and attacks on the IT Security – DoIT myUMBC group. In order to receive information as quickly as possible, we recommend that members of the UMBC community follow our group. Once followed, any new articles and notices will be automatically sent to the subscriber via email and myUMBC notification.
How to Follow
- Go to the IT Security myUMBC group
- Make sure you are logged into myUMBC.
- Click the Follow button, and select Notifications to All Updates.
Contact Info
To report a cybersecurity issue or get assistance with a cybersecurity topic, Submit an RT Ticket or email security@umbc.edu.
You may also contact the Technology Support Center (TSC) – 410.455.3838